Everything your team needs to stay ahead of incidents
Arca replaces your logging stack and your security stack in one self-hosted platform. Collect and search logs from 18 agents. Detect threats with 6 SIEM rule types. Investigate with autonomous AI. Manage cases with full SOC workflow. Simulate attacks. Generate compliance reports. All for $0 per GB.
Download a pre-configured agent package from Arca. Drop it on any Linux host, macOS machine, or cloud environment. Agents begin streaming data immediately — no manual configuration of API keys or collection identifiers required.
Logs and metrics land in named collections with your schema. Arca indexes up to 55 fields per document for fast querying. Full-text search works out of the box across all indexed fields.
Six SIEM rule types run continuously. When a rule fires, an autonomous AI investigation launches immediately — examining log data with 6 read-only tools, mapping to MITRE ATT&CK techniques, assessing severity, and producing a structured report. Cases are created with full SOC workflow. Response agents can automatically block IPs, disable accounts, kill processes, restart services, or revoke AWS sessions. You get notified via Email, Slack, or PagerDuty.
18 pre-built agents cover Linux, macOS, cloud, containers, and common services out of the box.
Six rule types cover the detection patterns that matter most — from brute-force attempts to statistical drift.
More than N events within M minutes. Detects brute-force, scan activity, and error bursts.
No data from a known source within M minutes. Heartbeat and host-down detection.
A previously unseen value appeared. Catches new source IPs, unexpected processes, unknown users.
Metric average changed more than N% between two time windows. Rate-of-change detection.
Value deviates from rolling mean by more than N standard deviations. Statistical outlier detection.
Multiple conditions combined with AND/OR logic. Correlated multi-signal detection.
Most monitoring tools give you data. Arca gives you an autonomous analyst. Every rule trigger launches an AI investigation — powered by Claude — that examines your log data with 6 read-only tools, identifies the attacker, maps to MITRE ATT&CK techniques, assesses severity and confidence, and produces a structured report with specific recommendations. An AI chat assistant embedded at every collection and namespace level lets your team ask follow-up questions in plain English. And every hour, Arca writes an AI health digest summarizing the state of each namespace.
This isn't a chatbot bolted on as an afterthought. Arca's AI has full context of your schema, your data, your detection rules, your active anomalies, and your investigation history. It's a conversation about your infrastructure, backed by autonomous action.
The autonomous investigation has already answered this. Open the investigation report to see the identified attacker, MITRE ATT&CK technique mapping, severity assessment, and recommended response actions — or ask the chat assistant for more detail.
Response agents can take autonomous action — blocking IPs, disabling accounts, killing processes, restarting services, or revoking AWS sessions. Cases track investigations through a full SOC workflow from triage to resolution.
The assistant understands your collection schema and data patterns. It can recommend specific alert thresholds and event rule configurations based on what it sees.
Every collection schema, every document, every alert rule, and every anomaly is structured to be AI-readable. When you open a chat, there's no loading, no context-switching — the model already has everything it needs to be useful. We built Arca this way intentionally, because we believe the future of infrastructure monitoring isn't better dashboards. It's better conversations.
Anthropic's Mythos model discovered tens of thousands of zero-day vulnerabilities in real-world software — autonomously. Comparable capabilities will proliferate to threat actors within months. When attacks move at machine speed, human-only detection and triage become the weakest link. Arca's autonomous investigation and response pipeline was built for exactly this moment: every alert investigated by AI, response actions in seconds, and continuous validation through Nemesis attack simulation.
Read our full analysis: Mythos Is the Warning Shot →When a SIEM rule fires, Arca doesn't just send a notification. It launches an autonomous AI investigation powered by Claude. The investigation examines your log data using 6 read-only tools, identifies the attacker and affected systems, maps the activity to MITRE ATT&CK techniques, assesses severity and confidence, and produces a structured report with specific response recommendations. Investigations complete in 60–120 seconds, not hours.
This is the detection-to-investigation loop that SOC teams have always wanted but never had — running 24/7, on every alert, without fatigue or alert blindness.
The AI queries collections, correlates events, checks threat intelligence, builds timelines, assesses severity, and analyzes entity activity — with read-only access that cannot modify your environment.
Every investigation produces a report with severity, confidence score, identified entities (IPs, users, processes), MITRE ATT&CK technique mapping, and actionable recommendations.
5 response adapters execute automatically or on-demand: block IP (iptables/UFW), disable user account, kill process, restart service, revoke AWS IAM session. Configurable per namespace.
Investigations automatically create cases with full SOC workflow — new, triaged, in_progress, resolved. Assign analysts, add comments, track audit trail, print to PDF.
When an AI investigation identifies a confirmed threat, Arca doesn't wait for a human to act. Autonomous response agents execute containment actions within seconds of detection — blocking attackers, isolating compromised accounts, and stopping malicious processes before damage spreads. Every action is logged with full audit trail and tied to the originating investigation and case.
Response actions are configurable per namespace with blast-radius controls, so you define what Arca is allowed to do autonomously and what requires human approval. This is real autonomous defense — detect, investigate, and respond at machine speed, 24/7.
Automatically add attacker IPs to iptables or UFW deny rules. Blocks take effect instantly and persist until manually removed or auto-expired.
Lock compromised user accounts at the OS level. Prevents lateral movement using stolen credentials while the investigation proceeds.
Terminate malicious or suspicious processes by PID. Stops active exploitation, cryptominers, reverse shells, or runaway processes immediately.
Restart compromised services to clear injected code or restore from a known-good state. Useful for web servers, databases, and application processes.
Immediately invalidate active AWS sessions for compromised IAM users or roles. Cuts off cloud-level access before resources can be exfiltrated or destroyed.
Define which response actions are allowed per namespace. Set auto-execute for high-confidence threats or require human approval — you control the boundaries.
Claude Sonnet embedded in every collection and namespace. Ask natural-language questions about your data. Full context: schema, recent documents, active anomalies, configured rules.
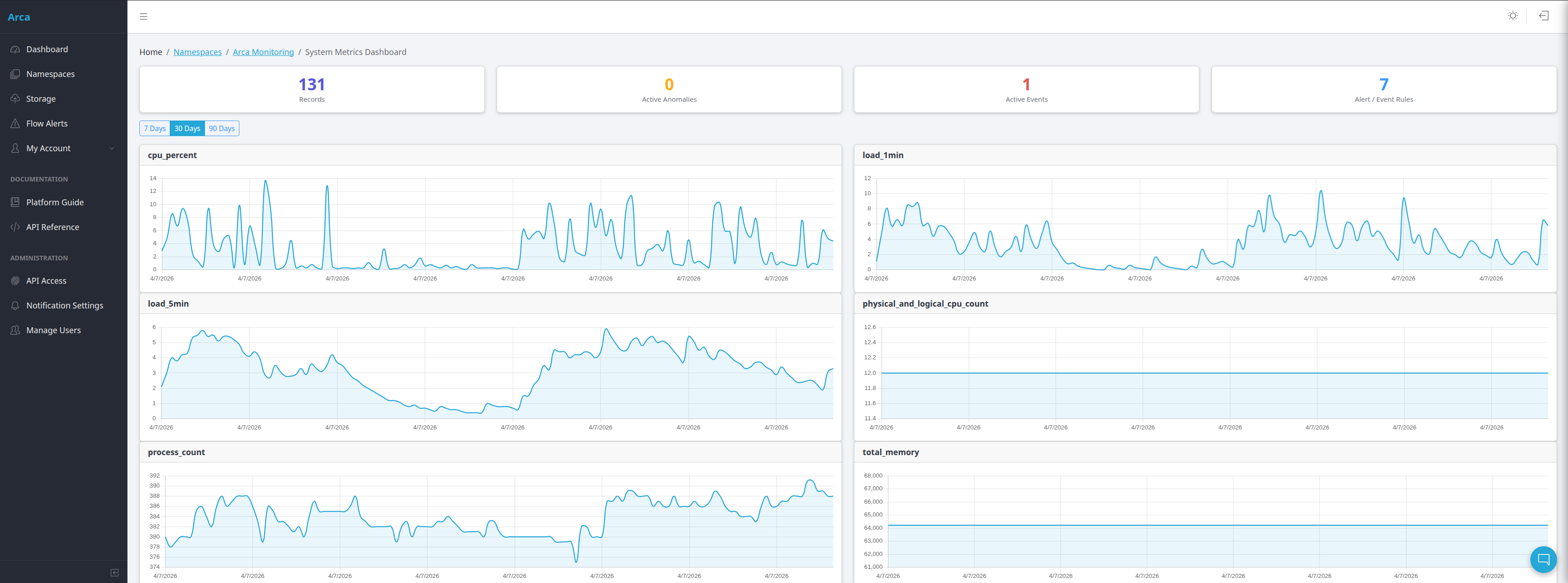
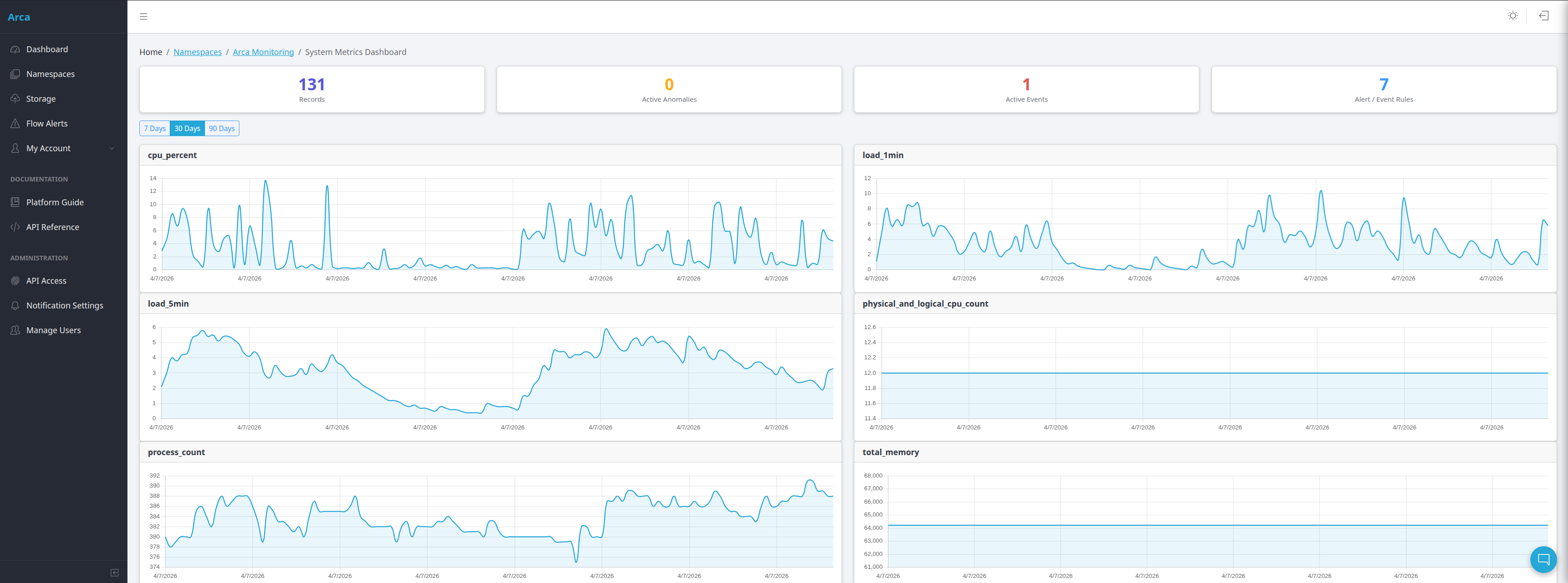
Every collection gets a dashboard automatically — time series charts with anomaly overlays, word clouds for text fields, and severity-coded markers. No chart building required.
Email, Slack, and PagerDuty — all individually toggleable per alert rule. Threshold alerts fire synchronously on write. Event rules evaluate every 60 seconds.
Case-insensitive substring search across all indexed fields, composable with partition filters and time range queries — from both the UI and the REST API.
Correlate fields from two or more source collections on a shared time bucket. Cross-collection dashboards and anomaly detection with no custom code.
Don't know your schema upfront? Send sample documents, let Arca discover the fields, review the suggestions, and confirm. Buffer-to-collection in seconds.
Complete API coverage: create namespaces and collections, write single or batch documents (up to 100), query with filters, and manage schema — all via API key.
Documents stored on your filesystem in configurable slices. Set per-collection expiration and compression thresholds. Storage monitoring built into the main dashboard.
Each agent type ships with curated alert and event recommendations pre-tagged with MITRE ATT&CK techniques. Review and create them in one click — no configuration from scratch.
64-technique taxonomy with coverage matrix visualization. Technique chips on every investigation report. See which ATT&CK techniques your detection rules cover and where gaps remain.
4 integrated feeds — CISA KEV, URLhaus, ThreatFox, AlienVault OTX — all free. Automatic enrichment of investigations with known indicators of compromise.
SOC 2 Type II, HIPAA, PCI DSS v4.0, and NIST CSF. Automated evidence evaluation from live platform data. Print-optimized auditor-ready reports.
Operational, Threat Intel, Executive, and Security dashboards. Pre-built views that give different stakeholders the data they need without custom configuration.
Leaflet-based geographic visualization of threat sources. See where attacks originate in real time, correlated with SIEM detections, AI investigations, and threat intelligence data.
Admin, analyst, read_only, engineer, and IT roles. Engineers and IT see log management only — SOC surfaces (investigations, cases, compliance) are restricted to security roles.
Nemesis is Arca's built-in breach and attack simulation engine. It runs 28 attack scenarios across 14 MITRE ATT&CK techniques, covering all 6 SIEM rule types. But Nemesis doesn't just check if a rule fires — it validates the entire detection chain: rule trigger, AI investigation launch, attacker identification, and technique classification. Grading happens at the investigation level.
Nemesis v2 goes further — it conducts real autonomous penetration tests against your infrastructure on an ongoing basis, not just as a one-time assessment. Schedule continuous pentesting as part of your security monitoring program, so your attack surface is validated regularly as your infrastructure changes. New hosts, new services, new configurations — Nemesis catches what drifts.
5-minute setup. No cloud account needed. No external tooling. Just run the scenarios and see what your detection coverage actually looks like.
Beyond simulation — real adversarial testing against your infrastructure with built-in safety controls.
Port scanning, banner grabbing, TLS certificate inspection, DNS enumeration, WHOIS lookups. Non-invasive discovery that maps your external attack surface without triggering defenses.
Credential stuffing against known services, CVE-based vulnerability checks, and configuration audits. Blast-radius limits and auto-abort ensure testing stays within defined boundaries.
Chains offensive actions with detection and response verification. Attacks are launched, detections are validated, response agents are triggered — a closed loop that proves your security posture end to end.
Arca doesn't just help you monitor — it helps you prove compliance. Built-in compliance reporting evaluates your detection rules, investigation coverage, response actions, and logging completeness against the specific controls required by major frameworks. Evidence is pulled automatically from your live platform data. Reports are print-optimized and auditor-ready.
Stop assembling compliance evidence manually from screenshots and spreadsheets. Arca generates the documentation your auditor expects to see.
15 Trust Services Criteria controls evaluated. Covers logical access (CC6), system operations (CC7), change management (CC8), and more.
13 implementation specifications evaluated. Administrative, physical, and technical safeguards mapped to platform evidence.
15 requirements evaluated. Emphasis on logging (Req 10), vulnerability testing (Req 11), and access control (Req 7-8).
13 categories across Identify, Protect, Detect, Respond, and Recover. Gap analysis with maturity scoring on a 1–5 scale.
Arca integrates with 4 curated threat intelligence feeds — all free, no subscriptions required. Indicators of compromise are automatically correlated with your investigation data and surfaced as "Known Threat" badges on investigation reports. The Attack Map provides a Leaflet-based geographic visualization of threat sources.
Feeds sync automatically every 6 hours. Admin UI for feed management and manual sync.
Full-page Leaflet-based world map showing geographic origin of detected threats. Attackers appear as pulsing red dots, targets as blue dots, with smooth bezier attack vectors color-coded by severity. Hover popups show IP, city, country, ISP, and linked investigations. Opens from any investigation page.
Operational (storage, ingest, agent performance), Threat Intel (feed health, indicator trends), Executive (KPIs, resolution time, platform value), and Security (MITRE heatmap, kill-chain depth, risk ranking). Time-window filters from 7 to 90 days.
We're onboarding teams now. Arca is self-hosted, with no per-GB billing. To get started, send us an email with a brief description of your infrastructure and security needs and we'll be in touch within 24 hours.
Request Beta Access Ask a Question